Understanding Deep and Shallow Copy in Java
In Java, deep copy and shallow copy are two ways of copying objects. The main difference lies in…... Read more.
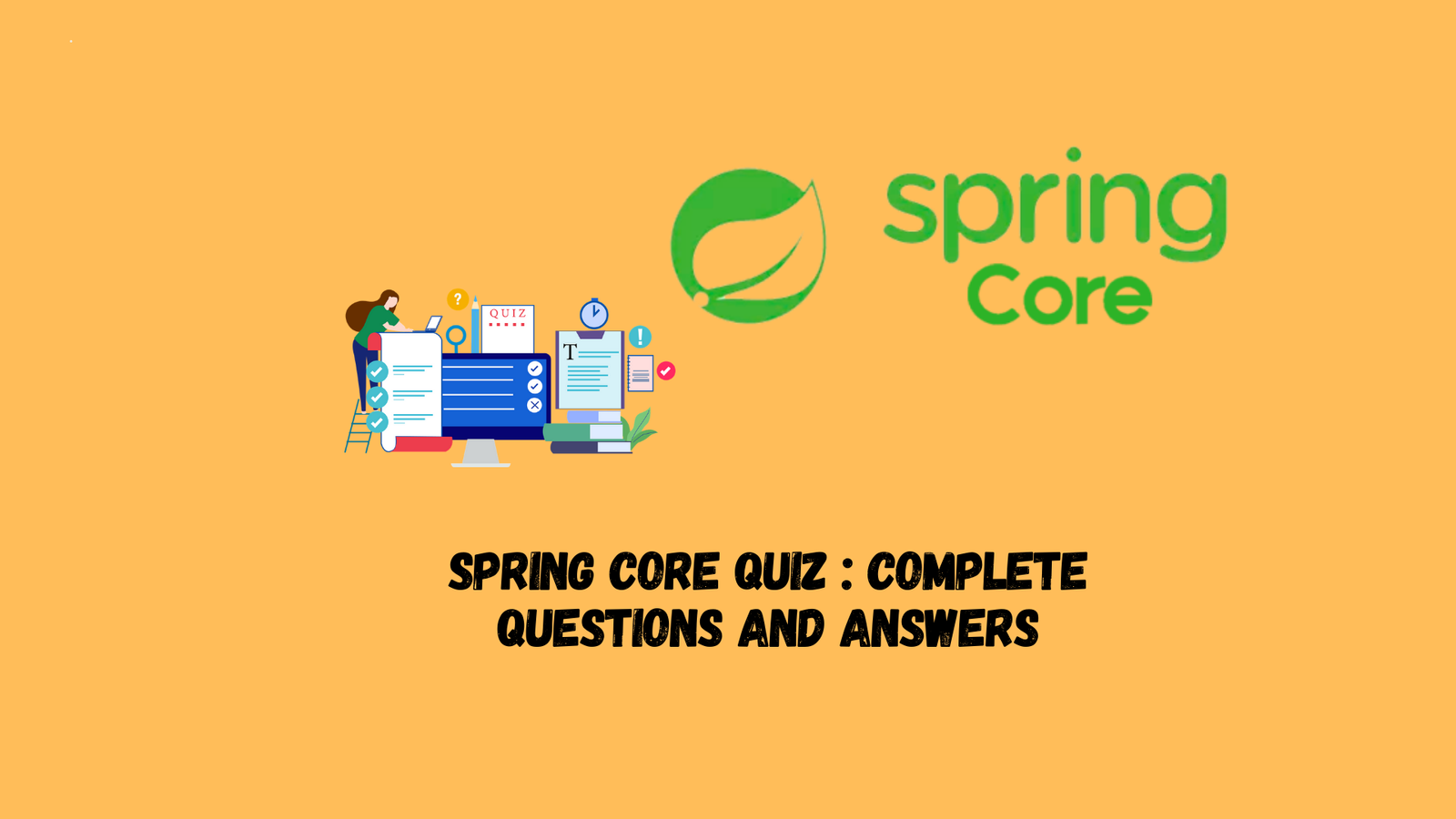
K8s Production Best Practices – Limiting NameSpace Resource Usage
Introduction Imagine this scenario: multiple systems are running on the same K8s cluster, including important systems and less…... Read more.

How to Use GIT Cherry-pick
Overview Regardless of the size of the project, when you work with a group of programmers, it can…... Read more.
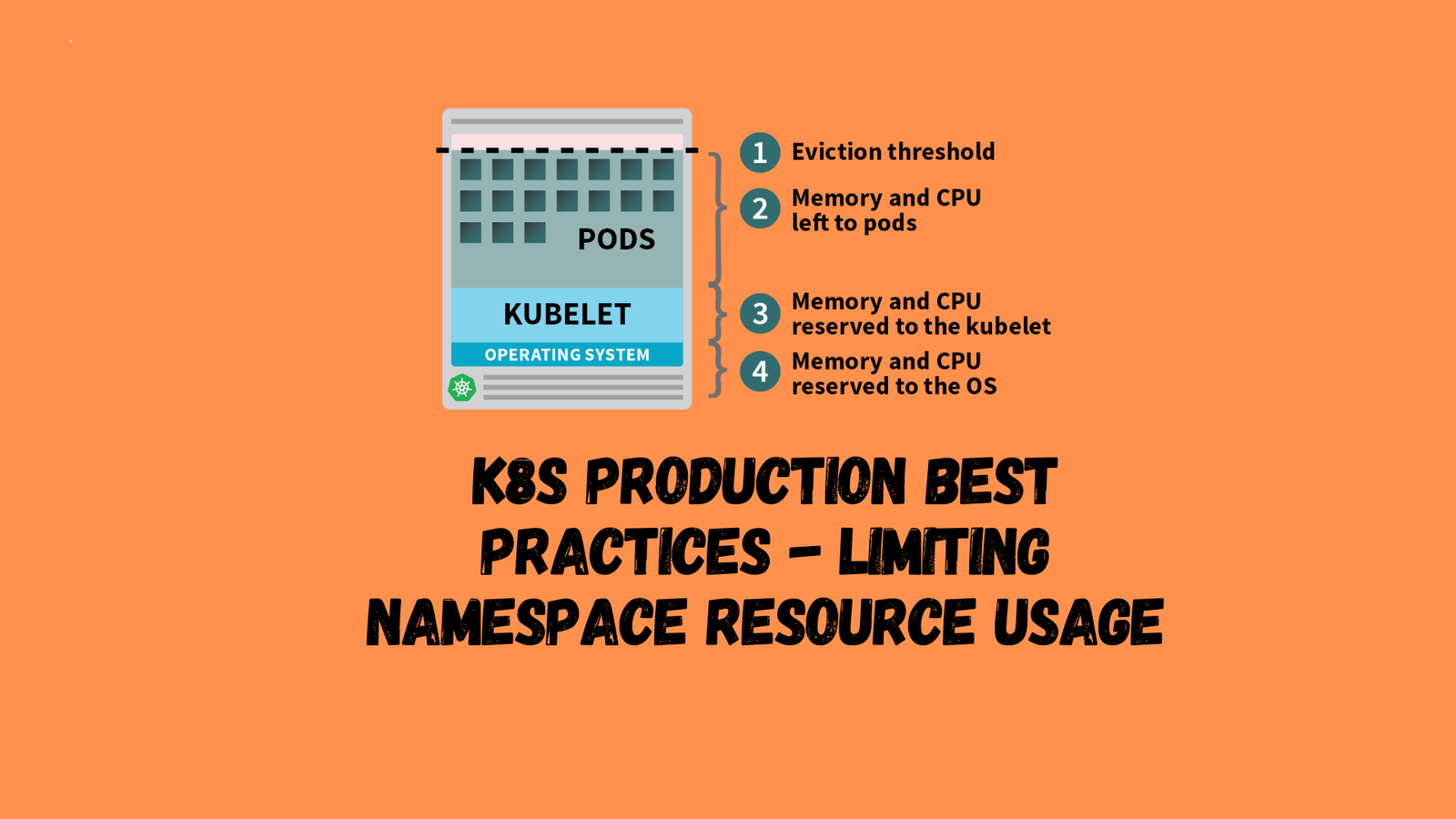
Kubernetes Security : Trivy to Scan Docker Images
In this article, we’ll explore how to use Trivy to scan Docker images, ensuring a secure environment for…... Read more.

It took 7 years to bring virtual machines into the Kubernetes world
With the development of cloud computing and container technology, Kubernetes has become the industry standard and leader, providing…... Read more.

How to Encrypt Kubernetes Secrets ?
Introduction You’ve probably heard this not-so-secret secret many times – Kubernetes Secrets are not encrypted! The value of…... Read more.

LangChain : Getting Started Guide
In daily life, we mainly focus on building end-to-end applications. There are many automated machine learning platforms and CI/CD…... Read more.